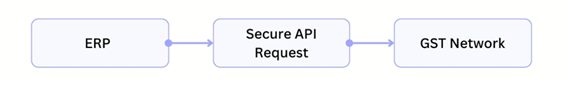
The average GST invoice moves through hundreds of touch points across the organization and beyond. Its journey begins from an ERP and then travels through integration layers to reach the Invoice Registration Portal and return with an IRN.
The GST invoice then flows into reporting systems and audit trails where transmission of regulated financial data is transmitted thousands of times each day in large enterprises.
However, large enterprises often overlook these facts about invoices while designing their GST compliance infrastructure. They tend to exclusively focus on automation or reporting capabilities. As a result, the integration layer that carries compliance data between enterprise systems and GST networks receives far less attention.
That layer quietly determines something far more important than convenience.
It determines how securely tax data moves across the enterprise stack.
For example, if a large FMCG company generating 50,000 invoices daily relies on delayed batch uploads, it is doing so at the risk of missing compliance timelines.
As GST adoption expands across India, this architectural decision is becoming increasingly important.
The Expanding Scale of India’s E-Invoicing Ecosystem
India’s e-invoicing framework has blown up far beyond what it was planned for. When the current system was first introduced, the mandate was applicable only for the handful of India’s largest enterprises.
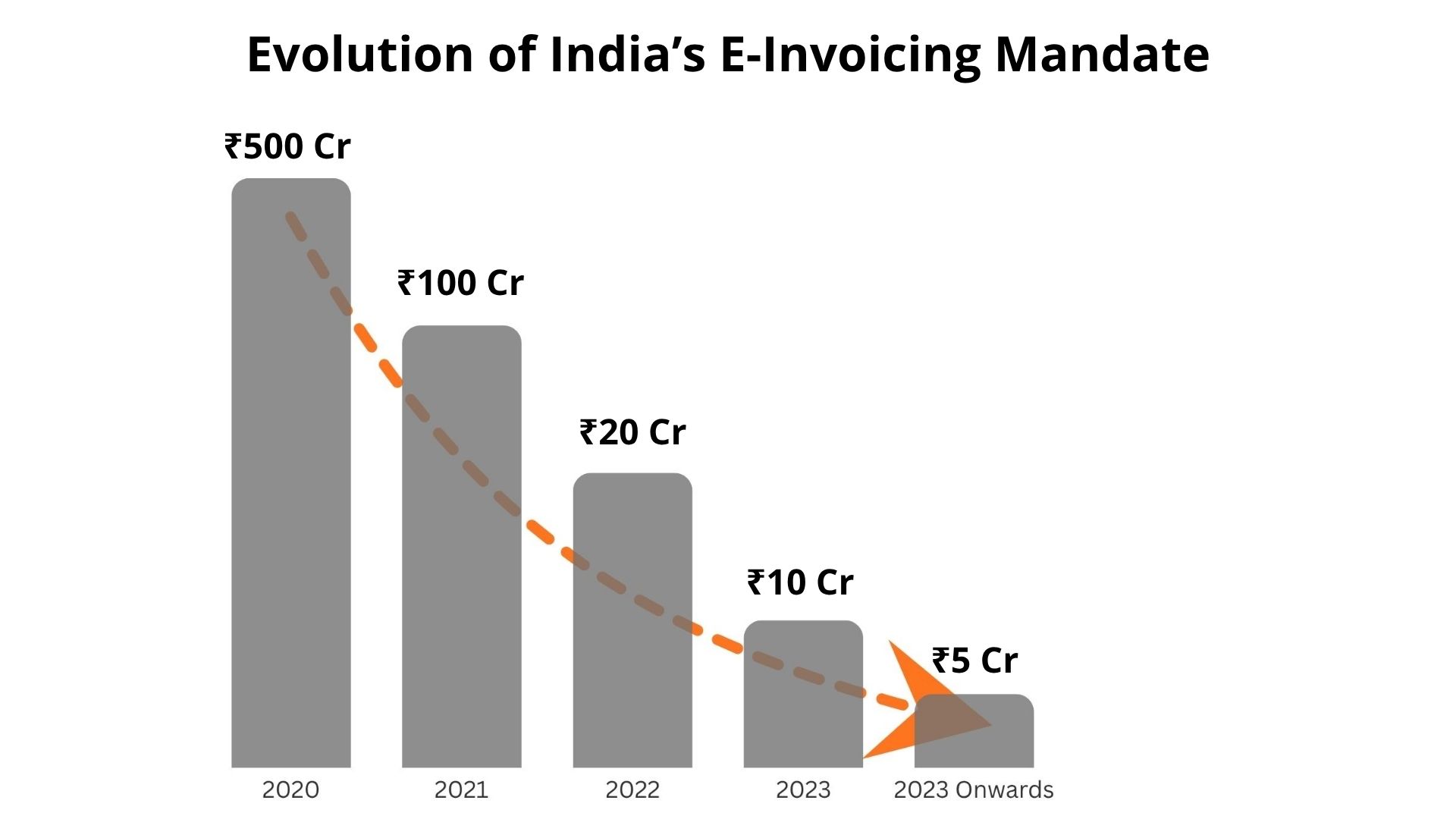
However, the revenue threshold has reduced in phases over the last few years pulling more businesses within the compliance network.
Today, the GST infrastructure is overwhelmed with more than 13 lakh GSTINs transmitting invoice data throughout the compliance network.
The turnover threshold has dramatically changed where organisations with an annual turnover exceeding ₹5 crore are required to comply with GST compliance requirements that were once applicable only for companies with more than a ₹500 crore annual turnover.
The evolution of the e-invoicing mandate clearly shows how rapidly the ecosystem has expanded, with the eligibility threshold gradually reducing over the years.
Today, compliance requirements are more stringent that ever before. Businesses with turnover above ₹10 crore are required to submit invoices on the Invoice Registration Portal within 30 days of the invoice date. Invoice data is typically transmitted over TLS-encrypted channels to the Invoice Registration Portal (IRP) via GSTN APIs.
These developments have increased the volume and frequency of data transmission between enterprise systems and GST infrastructure. As a result, the integration layer that carries this data has become a critical part of compliance operations.
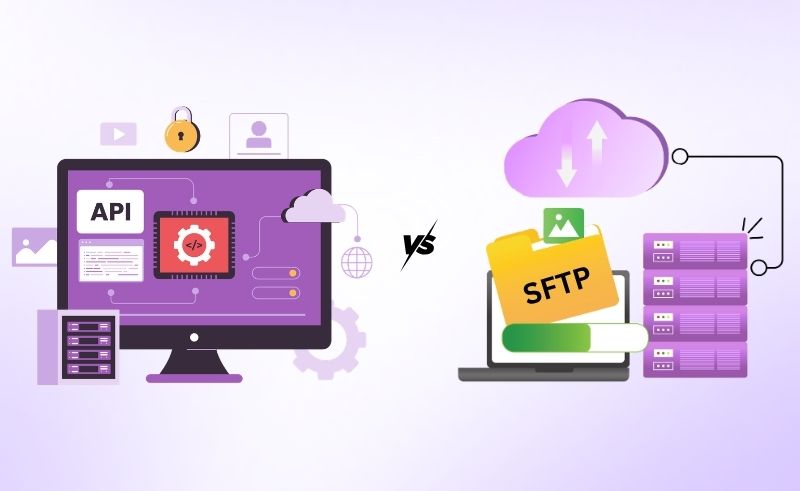
Two Ways GST Data Typically Travels to the GST Network
Most automated GST environments rely on one of two integration approaches. SFTP uses SSH-based encryption to secure file transfers in transit.
SFTP-based integration
In this model, enterprise systems export invoice or return data as files. These files are transferred through secure file servers before being processed and submitted to GST systems.

API-based integration
In an API architecture, enterprise systems communicate directly with GST infrastructure through secure request-response connections. Each transaction moves as structured data in real time rather than through batch files.
Both models enable GST automation. The difference lies in how data flows through the system and how securely that information travels across the integration pipeline.
Data is typically transmitted over TLS-encrypted channels to the Invoice Registration Portal (IRP) via GSTN APIs.

How SFTP-Based GST Integration Works
Since file transfer mechanisms have been the staple for enterprise system integrations, initially GST automation followed the same pattern.
Here’s how a typical SFTP workflow looks like. The ERP systems generated invoice data and converts it into either a JSON or CSV file format. The file is then uploaded to a secure file transfer server from where a compliance platform retrieves it to process the data and sends it to GST systems for validation.
This approach works well for batch processing environments where data moves at scheduled intervals.
Many organizations implemented their GST infrastructure using this model during the early adoption phase because it aligned with traditional enterprise integration methods.
However, as transaction volumes increase, operation complexities occur within file-based pipelines. Before a transaction file is sent to the GST network, it must be created, transferred, monitored, and processed.
Heavy transaction volumes create a strain on the file-based mechanism where delays or failures become unavoidable.
Where File-Based Transfers Introduce Security and Operational Risk
SFTP is widely considered secure because the file transfer channel itself is encrypted. However, the broader workflow includes several stages where sensitive compliance data may exist within the integration pipeline.
Key operational and security considerations include:
Multiple intermediate storage points
GST data is usually generated as files before transmission. These files may temporarily reside in export directories, SFTP servers, or processing systems before reaching the GST network.
Expanded data exposure surface
Every additional storage location becomes another point where invoice data, tax information, and customer details exist within the system environment. APIs reduce storage-based exposure but introduce runtime security considerations such as endpoint protection and rate limiting.
Credential management complexity
File transfer environments frequently rely on shared authentication credentials across systems. Managing access controls and credential rotation across these systems can become operationally demanding.
Delayed error detection
Batch processing means issues during file generation, or transfer may only become visible after the batch cycle completes, which can delay corrective action.
These characteristics do not make SFTP unsuitable. Many organizations operate stable file-based systems successfully.
However, as invoice volumes increase and compliance timelines become stricter, organizations often evaluate architectures that minimize intermediate handling of sensitive data.
How API Based GST Integration Changes the Architecture
API-based integration approaches the problem from a different direction.
Instead of generating files and moving them across servers, enterprise systems communicate directly with GST infrastructure through secure API endpoints.
When an invoice is generated inside the ERP, the system sends a request containing the transaction data to the GST network. The Invoice Registration Portal validates the request and returns the IRN response.
This exchange happens within seconds.
The process becomes a direct system-to-system interaction.
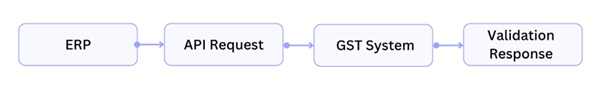
There are no intermediate files and no scheduled transfer cycles.
APIs do not store data. APIs themselves are communication interfaces, but underlying systems may temporarily store logs, queues, or payloads depending on implementation.
Security Advantages of Real Time API Infrastructure
API architectures introduce several security advantages for GST data transmission.
Reduced intermediate storage
Transaction data travels directly between systems instead of existing as files within multiple locations.
Stronger authentication controls
API environments typically use token-based authentication and controlled access policies, allowing technology teams to manage permissions more precisely.
Immediate validation
Errors are identified at the moment the transaction request is processed. This reduces the risk of delayed compliance submissions.
Better visibility into transactions
API integrations generate detailed request and response logs, which help organizations track transmission status and troubleshoot issues quickly.
For companies operating high-volume billing environments, these characteristics provide greater operational control over compliance data flows.
Why Integration Architecture Is Becoming a Strategic Decision
For many years, GST compliance systems functioned as reporting tools that operated at the end of the transaction cycle.
That’s not the case today.
E-invoicing now sits directly within the transaction flow of enterprise systems. Every invoice must pass through the GST infrastructure before it becomes a finalized document.
When thousands of invoices are generated each day, the integration pipeline becomes an operational dependency.
A delay in transmitting invoice data can affect billing cycles. Integration failures can disrupt compliance reporting. Security exposure within tax systems can introduce regulatory risk.
For these reasons, organizations reviewing their GST infrastructure are paying closer attention to the architecture that connects their ERP systems to the GST network.
(Also Read: GSTR-1 & GSTR-3B Reconciliation Errors and How to Automate Them)
Where Pass Through API Models Strengthen Data Security
Another architectural factor often overlooked is how compliance platforms handle transaction data during transmission.
In many file-based environments, compliance data exists within multiple layers before it reaches the GST network.
However Pass-through architectures reduce persistent storage, but do not completely eliminate transient handling (logs, retries, audit traces).
Pass-through API models reduce this exposure.
In this architecture, the platform functions as a secure communication bridge between enterprise systems and GST infrastructure. When an ERP generates invoice data, the information moves through encrypted API requests directly to the GST network.
Because the platform acts as a transmission layer rather than a storage layer, the data does not remain within the system once the request is processed.
Reducing the number of locations where compliance data exists can significantly lower exposure risk for organizations handling sensitive financial information.
Which Integration Model Provides Stronger Security?
A simple comparison helps illustrate the architectural differences between the two integration models.
| Factor | SFTP-Based Integration | API-Based Integration |
|---|---|---|
| Data Transmission | File transfer through SFTP servers | Direct request-response communication |
| Data Handling | Requires file generation and intermediate storage | Data moves directly between systems |
| Processing Model | Batch-based processing | Real-time transaction processing |
| Error Detection | Issues may appear after batch cycles | Errors identified immediately |
| Authentication | Typically credential-based access | Token-based authentication mechanisms |
| Operational Visibility | Limited monitoring across file transfers | Detailed request and response tracking |
Both SFTP and API-based integrations can support GST compliance. The difference lies in how data moves through the system.
File-based integrations rely on generating and transferring files across multiple stages before the data reaches the GST network. API-based integrations allow enterprise systems to communicate directly with GST infrastructure through secure request-response connections without creating intermediate files.
As invoice volumes grow and reporting timelines become stricter, many organizations are shifting toward API-driven architectures that provide a more direct and controlled path for transmitting compliance data.
Supporting Secure GST Connectivity with Excellon Exact
Organizations evaluating GST integration infrastructure often look beyond basic automation features. The underlying architecture that carries compliance data becomes equally important.
Excellon Exact operates as a SAP certified GST Suvidha Provider (GSP) and enables enterprises to connect their ERP environments with GST infrastructure through secure pass-through API.
The platform supports a pass-through integration model, allowing transaction data to move between enterprise systems and the GST network through encrypted communication channels.
For organizations managing high invoice volumes, this architecture provides a reliable mechanism for transmitting compliance data while maintaining control over how that data flows across systems.
Encryption Standards
GST data transmitted via APIs is typically secured using TLS 1.2 or higher, ensuring encryption in transit. In SFTP-based systems, encryption is provided through SSH protocols.
However, organizations must also ensure encryption of data at rest, especially in file-based workflows where invoice data may be temporarily stored.
Audit Trail Requirements
A robust audit trail is essential for GST compliance, ensuring end-to-end traceability of every invoice—from ERP generation to IRP submission, IRN generation, and final reporting.
Systems should maintain immutable, timestamped logs that capture all actions, including:
- Creation
- Modification
- Cancellation
- Submission
These logs must also include user or system identification.
For API-based integrations, detailed request–response logs—including payloads and error messages—are critical.
Additionally, version control must be enforced so that any changes to invoices are recorded as new events rather than overwriting original data. This enables accurate reconciliation and audit verification.
Data Retention Policies
GST regulations require businesses to retain records for at least six years from the due date of the relevant annual return, making structured data retention policies crucial.
Organizations should securely store both raw and processed data, including:
- Original invoices
- IRN details
- Acknowledgements
This data must be protected with encryption at rest and strict access controls.
An effective archival strategy should:
- Move older data to secure storage
- Keep it easily retrievable for audits or regulatory checks
At the same time, businesses must define clear data deletion policies post-retention, ensuring compliance with internal governance standards while maintaining consistency across ERP systems, compliance platforms, and reporting systems.
GST Audit Readiness
GST audit readiness depends on the ability to quickly reconcile and present accurate data across systems, including:
- ERP records
- IRP-generated IRNs
- GST returns such as GSTR-1 and GSTR-3B
Organizations must ensure:
- Real-time visibility into errors, rejected invoices, and mismatches
- Easy access to supporting documents such as invoices, acknowledgements, and e-way bills
Strong audit readiness also requires:
- Comprehensive system logs
- Consistent data across filings
- Clearly defined internal controls for invoice processing and submission
Additionally, reliable backup and disaster recovery mechanisms are essential to ensure that compliance data remains available and intact during audits or system failures.
Contact Us
Understanding India’s GST 2.0 Reforms and Compliance Framework